Whilst everyone else in the UK is panicking over the results of the EU referendum, I decided, as usual to do something completely different. Here I’m going to review the Operating System designed for use by the citizens of the Democratic People’s Republic of Korea, or North Korea as it’s more commonly known.
Red Star OS is a very interesting system. Approved by the North Korean regime, the system was designed only for use in the country, with tools and software preinstalled for the people of the country, and preconfigured to work on DPRK’s isolated intranet.
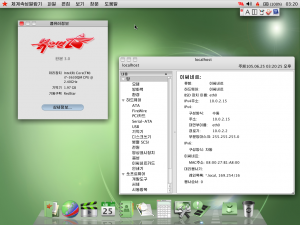
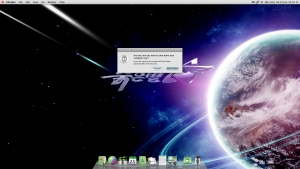
A quick look at the image above of my own laptop running Red Star OS 3.0 (in a virtual machine, of course), you can’t help but notice how much it looks like a typical Mac OS X system. This is not just from a front end point prospective, the whole system down to how files are arranged on the hard drive, and how software is saved on the system, emulate OS X. I am personally very impressed how well this system accurately replicates that OS X experience to the user. Unfortunately, Red Star also hides a nasty dark side from the user, but more on this later.
The OS X replication is actually a new feature for version 3 of the system with previous versions supposedly resembling Windows XP, the system still commonly used in DPRK. Personally, from screenshots, I think it looks like a slightly modified KDE 3.X desktop, which is exactly what it is. The intriguing thing about version 3 and its OS X likeness is that the system is still heavily based on KDE 3.X. But why go to all the bother of replicating OS X at all? The general consensus is that it’s down to a picture of the North Korean’s supreme leader, Kim Jong Un, at a desk with an iMac close by.
But enough talking, lets install this. Firstly, anyone else feeling brave enough can head over to this site and download, not only Red Star OS 3.0 Desktop, but also Red Star OS 3.0 Server, and Red Star OS 2. Once you have the ISO downloaded, you can either install it into a VM (Highly Recommended), or burn it to DVD and install it on physical hardware. I’ve opted to install it into Virtual Box. I can’t guarantee results on other virtualisation platforms, I can confirm the guest additions for Virtual Box will install on Red Star after a bit of tinkering.
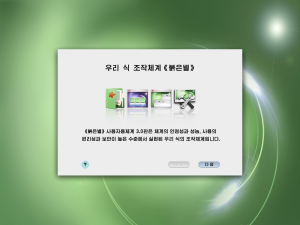
So, when first powering on the system, it takes a few minutes before we see anything, but eventually, this screen pops up. There is no option to switch the installer to anything but Korean language, so we have to guess everything we’re doing.
We have to create a user account, on this screen the boxes represent the following:
- Name (This is limited to 16 characters)
- Username
- Password
- Confirm Password
- Password Hint
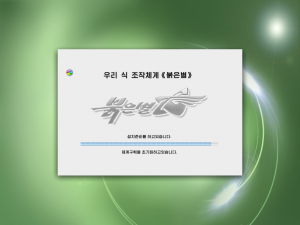
Now we sit back and let the installer do its thing. Time to grab a coffee.
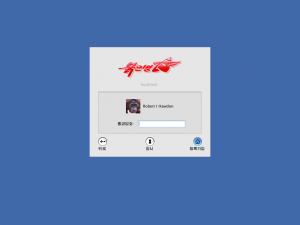
So we’re now ready to boot into our new shiny system. The installer automatically ejects the DVD and give the user 30 seconds before rebooting automatically. In a few brief moments, we’re presented with this login dialogue box.
Once we log in, we are presented with, for regular OS X users, a very familiar desktop, clicking the Red Star icon in the top left hand corner, we can select a menu item that represents the “About This Mac” function, which will allow us to look at what’s in this system.
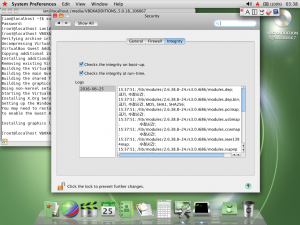
So, the first thing we want to do at this stage is to get the Virtual Box guest additions installed to allow for better integration. Unfortunately, this isn’t a simple task as system integrity is a big part Red Star OS. The system is known to complain when some files have been changed, or go into an endless reboot loop when system files have been modified. Parts of the system are protected by SELinux with some very specific rules. The system also watermarks files that have been opened (or accessed in any way, even if the user hasn’t actively opened it) on the system. The theory here is that any files that the regime doesn’t approve of can be tracked back to users have had a copy.
Thankfully, a couple of German hackers – Niklaus Schiess and Florian Grunow – explored the system in great detail and provide steps on disabling the security features. This can be found on their GitHub project page: https://github.com/takeshixx/redstar-tools
I had to deviate a little from their instructions as it’s not mentioned how to get Red Star to connect to the outside world to grab their scripts or source code. Fortunately, the libos library replacement source code is only 3 simple lines of code that can be easily rewritten by hand. Some tools also need to be installed after gaining root access. To do this, firstly disable the yum repo that points to /media/, as this causes issues with yum.
mv /etc/yum.repos.d/rs-core-03000.repo{,-disable}
Then enter the RPMS folder on the Red Star installation Disc:
cd /media/RedStar\ Desktop\ 3.0/RedStar/RPMS/
Finally, run the following to install the required packages:
yum localinstall glibc-headers-2.10.1-2.i386.rpm glibc-devel-2.10.1-2.i386.rpm ncurses-devel-5.6-0.rs3.0.i386.rpm gcc-4.4.0-4.i386.rpm kernel-devel-2.6.38.8-24.rs3.0.i686.rpm
I’ve included the Kernel development package here to allow us to install the Virtual Box guest additions. Once the dependencies are installed, and the steps in the github repo have been followed, we can change the system to use the English language. This is not an option that can be configured in the UI and requires the system’s protection to be disabled as mentioned above. Running the following will switch the system’s language:
sed -i 's/ko_KP/en_US/g' /etc/sysconfig/i18n
sed -i 's/ko_KP/en_US/g' /usr/share/config/kdeglobals
At this point we should reboot. Once restarted the system will be a lot easier to use. I assume the above commands can be modified for your own native tongue, but I haven’t tried this.
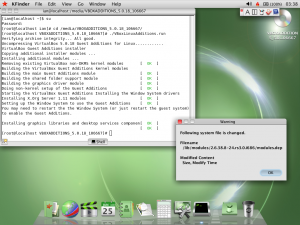
We can now go about installing the guest additions. We have to do this manually as Red Star, unsurprisingly, doesn’t include them in RPM form. Simply close your terminal (or change directory to a location outside of the DVD), eject the Red Star DVD from within the system, and select “Insert Guest Additions CD Image” on Virtual Box. After that, launch a new terminal and navigate to the Guest Additions mount point and run the Linux installation.
cd /media/VBOXADDITIONS_5.0.18_106667/
./VBoxLinuxAdditions.run
Installing the guest additions causes some files to be changed, which Red Star’s integrity checker picks up on and displays errors. The messages can be disabled from the security section in the system preferences.
Lets have a look at the applications included on the default install.
Here we see, right out of the box, Red Star comes with many useful applications: A full office suite, media player, web browser, pdf editor, text edit, sheet music editor, calendar, calculator, and email application, to name a few.
But lets look at the web browser in more detail.
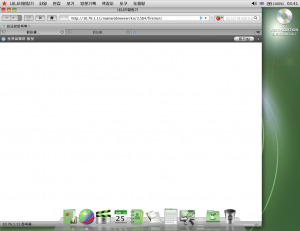
The Naenara web browser is simply a rebadged copy of Firefox 3.5b4. This is a particularly old release that debuted on 27th April 2009. This shouldn’t be too much of a security issue, as the web browser is only intended to be used within North Korea’s intranet.
In the screenshot, the Naenara browser, by default, doesn’t honour the system’s language settings. A few applications are like this. My best guess is that the software it’s based on doesn’t have Korean language support and require modifying to do so. In Naenara’s case, a Firefox extension has been installed which provides the Korean language support. A simple case of disabling the extension and restarting Naenara brings the interface up in English.
In the last two screenshots, you can see Naenara attempting to connect to a site under the IP address of 10.76.1.11, this appears to host the Naenara home page, but without being in North Korea, it’s impossible to tell for certain. Attempting to load any other web site results in an error saying the connection is unavailable. It turns out that Red Star has IPTables firewall rules set up to only allow communications within the DPRK’s intranet. This can be resolved by removing the firewall rules entirely:
rm /etc/sysconfig/iptables
service iptables restart
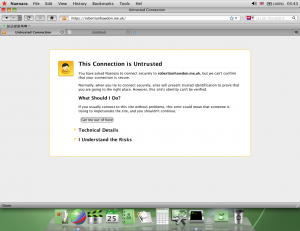
At this point, all unencrypted websites are accessible. This is fine until you try accessing a site served over HTTPS.
Every HTTPS site shows an error, this is due to Naenara not shipping with any of the root certificates apart from ones for internal communications within the country. Installing vanilla Firefox 3.5 onto the system allows you to access the sites without errors, apart from a few minor caveats which are most likely due to the age of the browser.
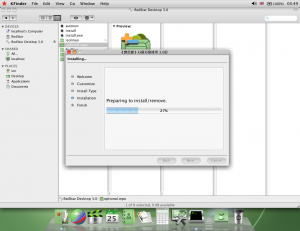
There are so many more things that can be said about this system, but I’m aware this post is already pretty long, so I’m going to wrap this up with a little bit about the optional components that can also be installed. Pop in your installation DVD again, and you’ll find a file called “optional.repo”. This will launch an OS X style installation window which will let you install a whole host of extra applications, console tools, and development libraries.
Once these are installed, the number of applications in the applications menu increases, and also includes a front end for installing Windows applications via WINE.
It’s uncertain how often the OS is updated and if any extra backdoors are included when the system updates. Without access to North Korea’s intranet this can’t be tested.
So, lets wrap this up by shutting down the machine. Again, the shutdown process replicates OS X. It seems strange that a government would go to the length of creating a whole system designed to snoop on its citizens, but these are the kinds of stories we’re used to hearing about coming from North Korea. A bit of advice, I wouldn’t use this as my primary operating system, for obvious reasons. But as for snooping, I’m highly doubtful that Red Star would be able to successfully snoop on any of my activity, as I’m almost certain that any spying it does do relies on the DPRK’s intranet being available.
Cheers
A big shoutout to the following sites where I got a lot of information from to get this up and running:
http://www.openingupnorthkorea.com/downloads-2
https://richardg867.wordpress.com/2015/01/01/notes-on-red-star-os-3-0/
https://github.com/takeshixx/redstar-tools